Hiding Caller ID is something else than changing phone number and depends on your cell phone and mobile network settings. The result is just a Unknown call received by the call recipient. Read more here.
|
Surprisingly for most people, the phone number (called MSISDN in terms of mobile networks) is not stored on SIM card, which contain only SIM ID, called IMSI (International Mobile Subscriber Identity). By consequence, there is nothing that can be changed locally in a secure way, on SIM level. This is why XCell Stealth Phones can change/manipulate IMSI and cannot directly change phone number.
Hiding Caller ID is something else than changing phone number and depends on your cell phone and mobile network settings. The result is just a Unknown call received by the call recipient. Read more here.
0 Comments
Test your "secure" phone. Now.Before everything, let’s face it: who do you really fear?
There are not so many hackers around that can actually track your cell phone, because of few simple reasons: expensive hardware needed, lack of knowledge regarding GSM stack and SS7 protocol effective exploits, not to mention that hackers have no interests on you, average Joe. Excepting your worried parents and jealous girlfriend, no one wants to know your (cell phone) geo-location. Tracking a cell phone is not a simple “push button” situation when is done by a hacker. That involve deep and extensive knowledge, pretty expensive hardware, time and not least, an considerable interest on you, average Joe. Which obviously is not the case unless you are just another skilled hacker or a high profile person. The situation became serious when you did something bad or even illegal. Then, you became a target for law enforcement and/or intelligence agencies. And there is no way to hide your (cell phone) location. They have not only the legal ability to track down your cell phone at any time, but have also technological and human resources to do that, not to mention training and expertise. In case you think that your own cell phone is secure, its time for 2 simple tests. TEST No. 1: NETWORK TESTING BY EMERGENCY CALL. Read more here. XCell Stealth Phones: a new website and new productsTo be honest with you and also with XCell guys, their old website doesn't look too nice. In fact the look was pretty obsolete with that old HTML version. But now everything is changed and you can navigate on a brand new web shop: https://stealth-phones.com
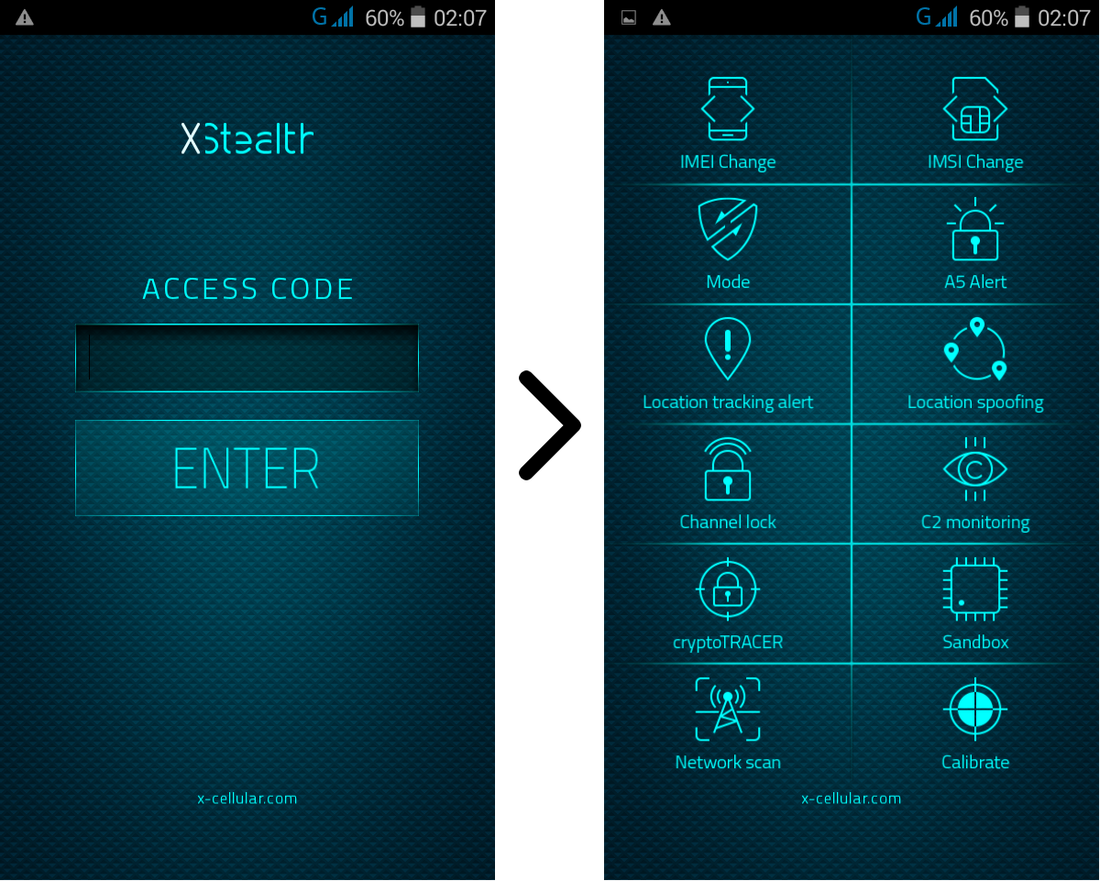
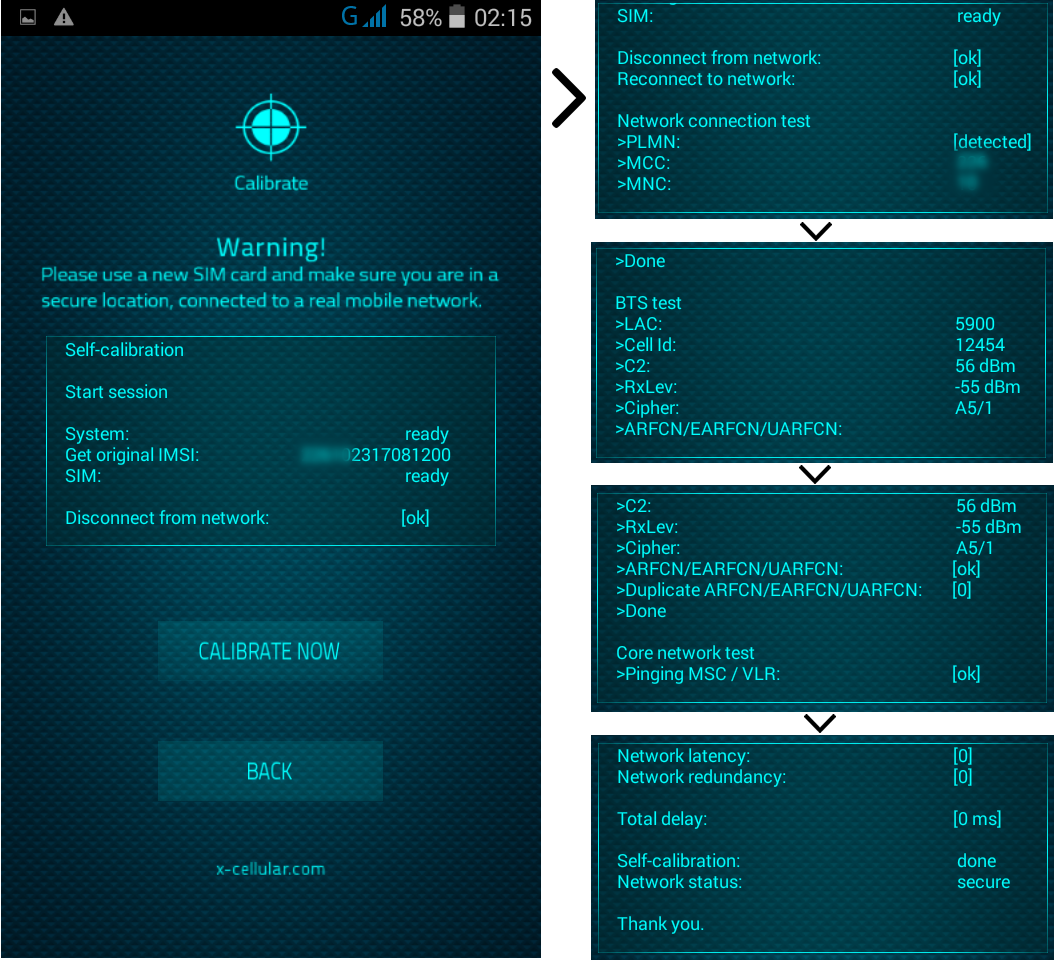
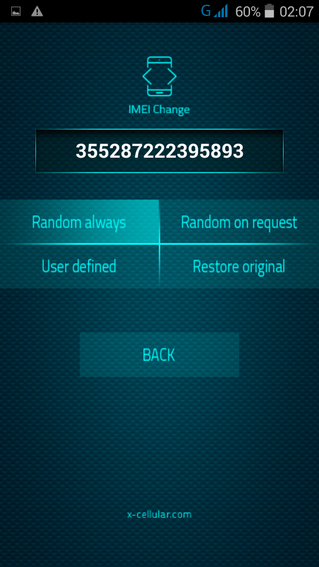
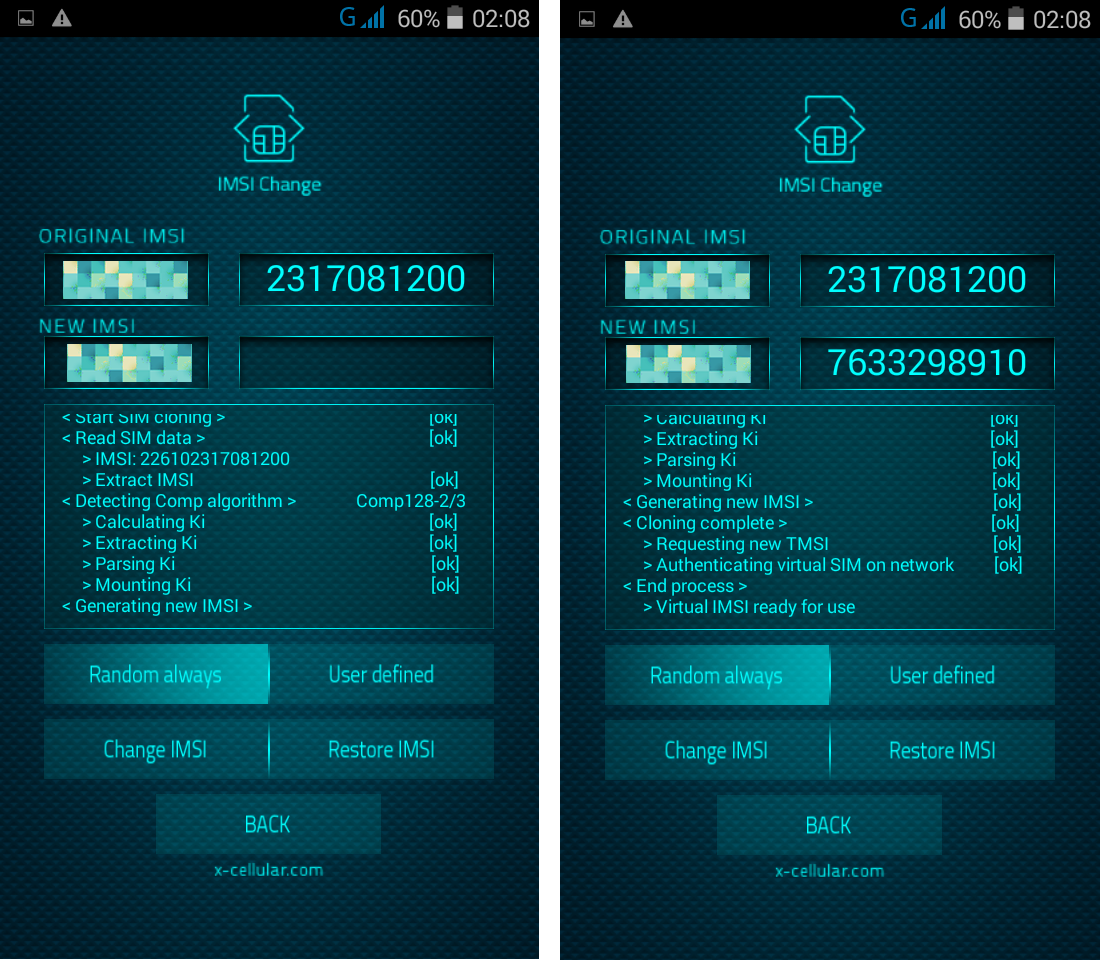
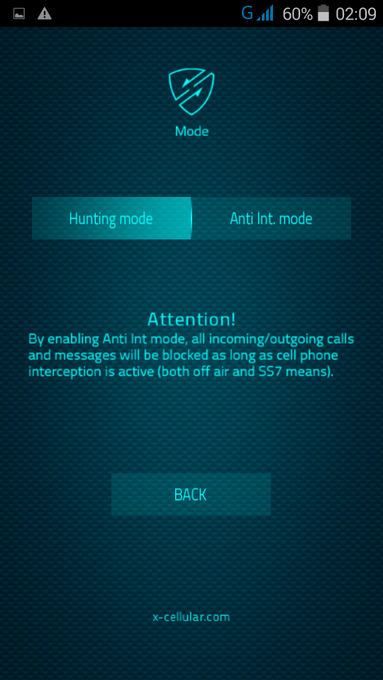
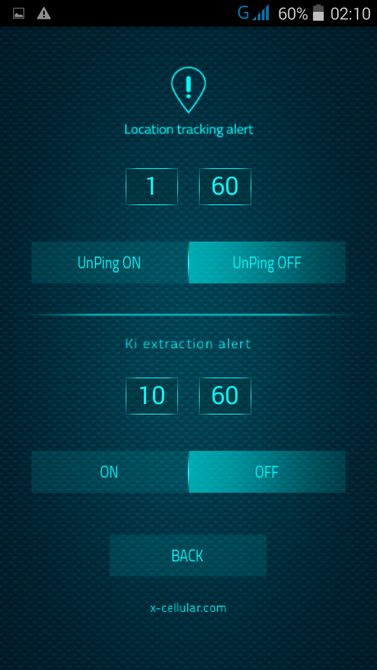
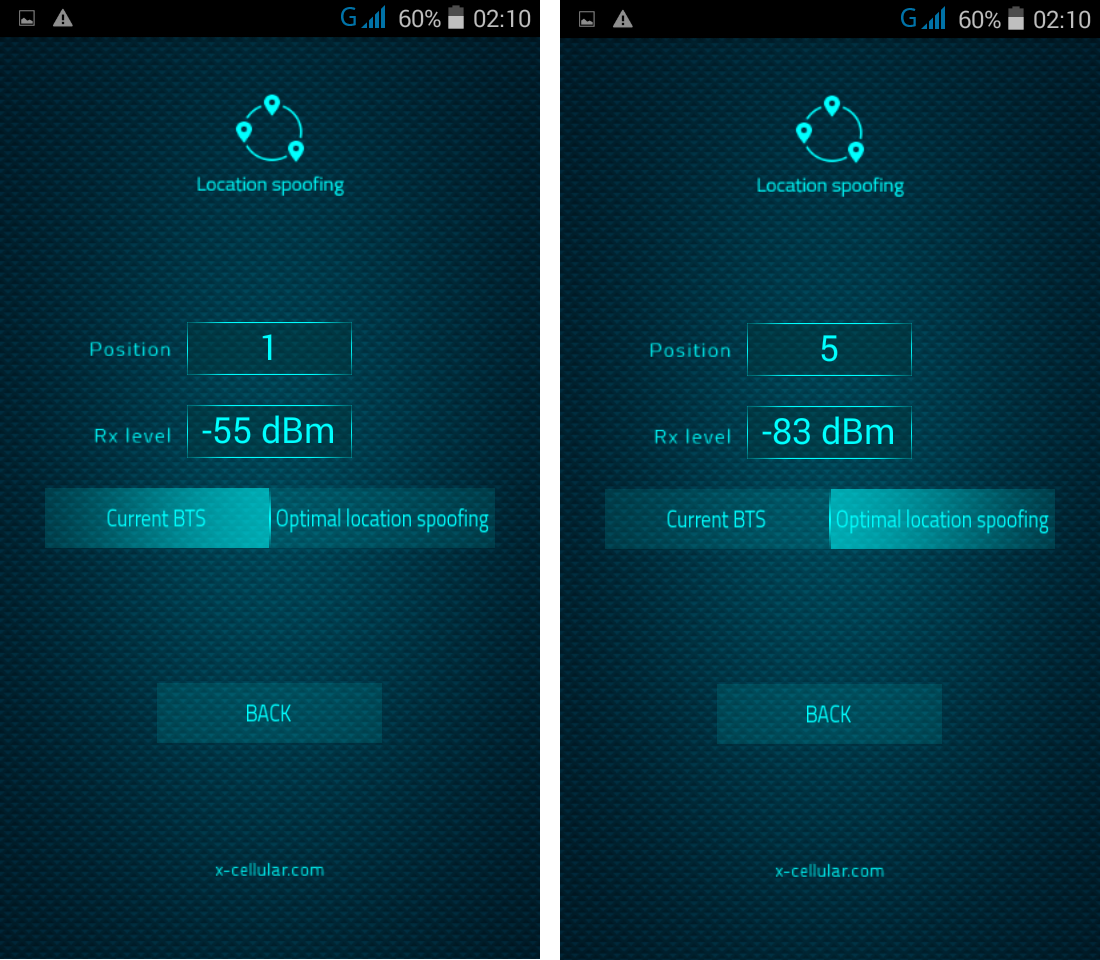
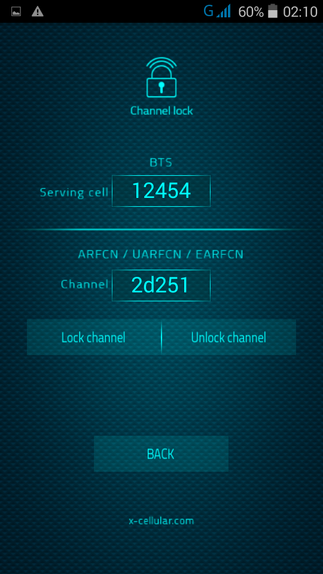
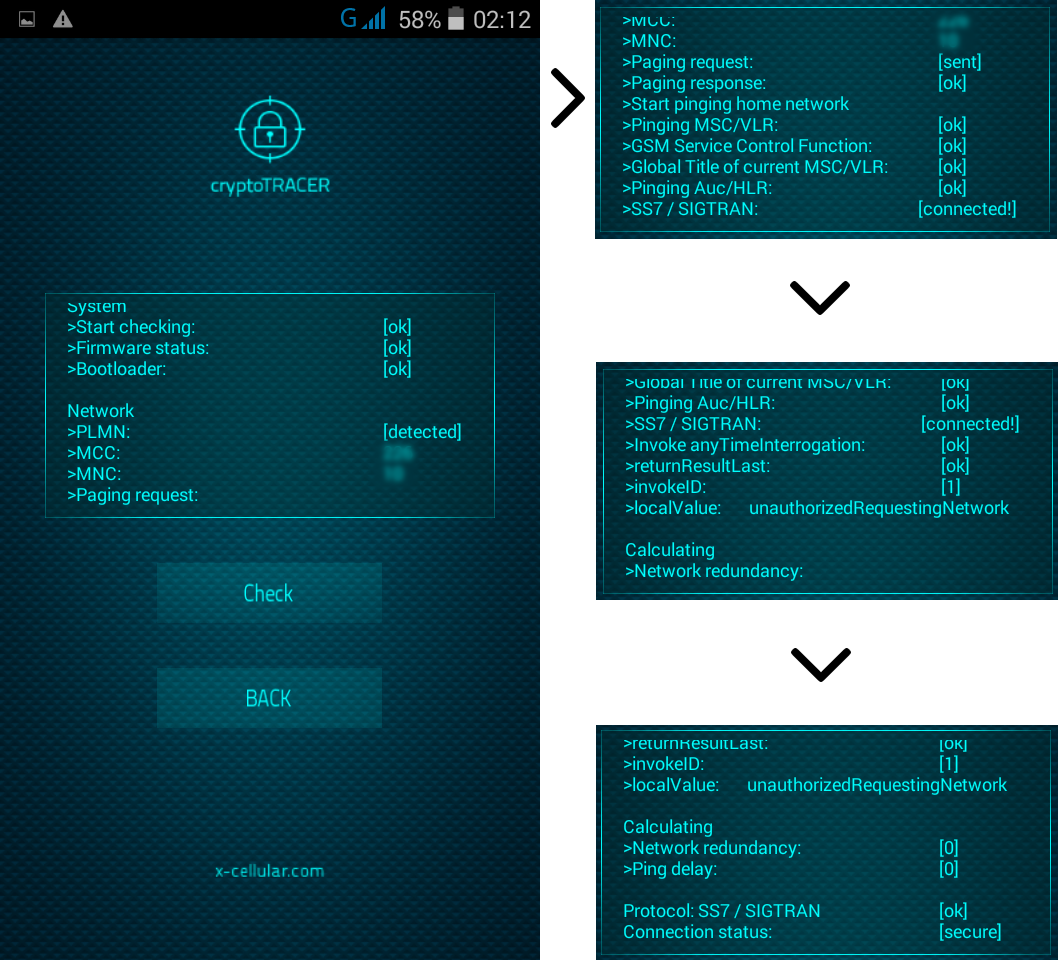
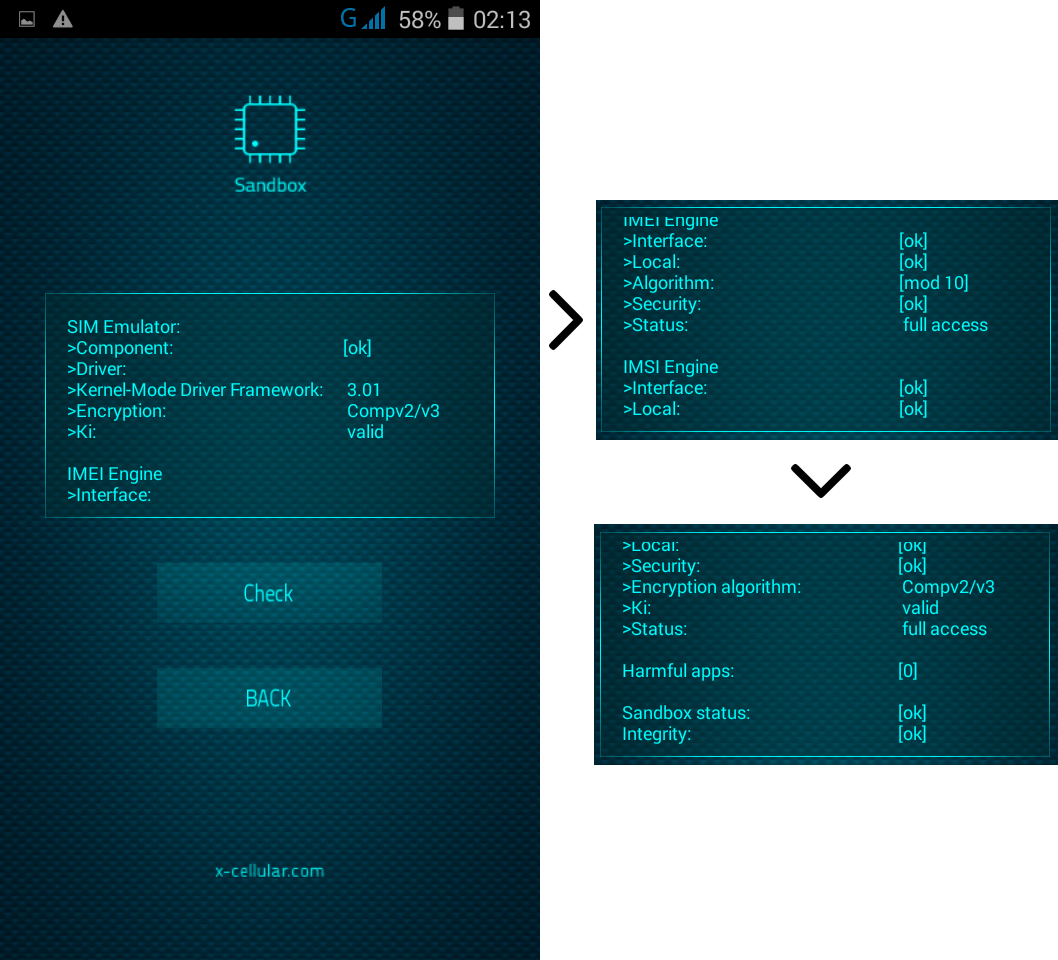
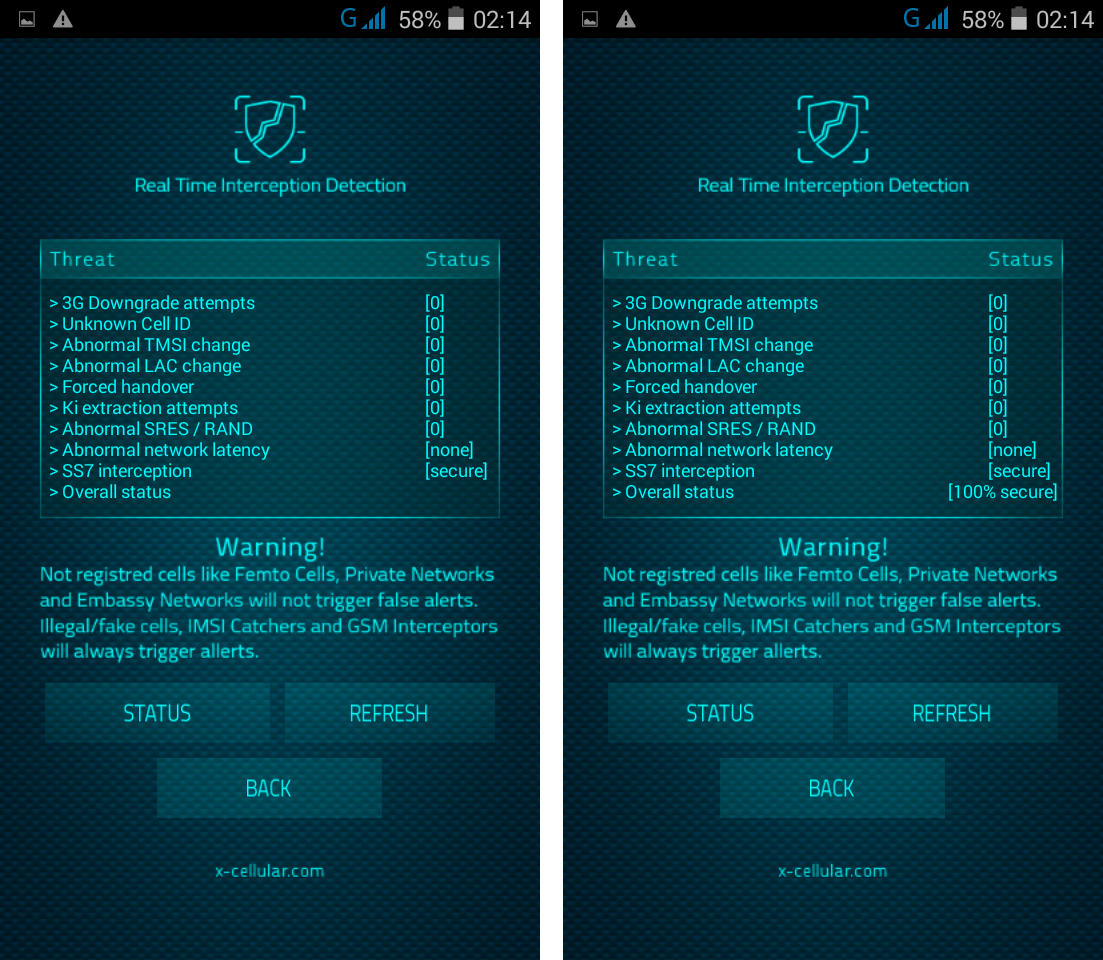
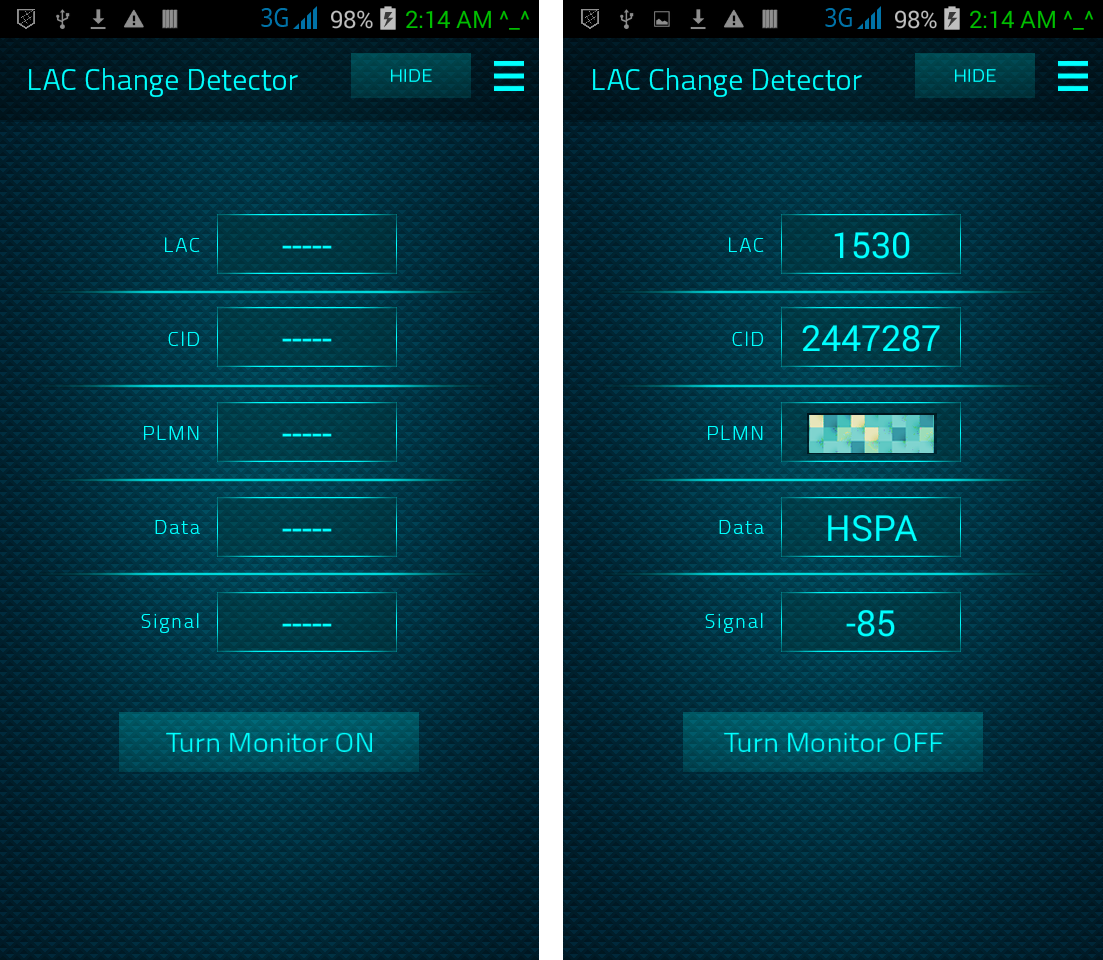
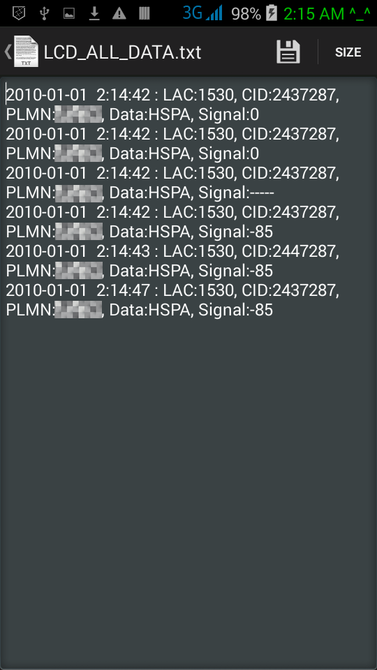
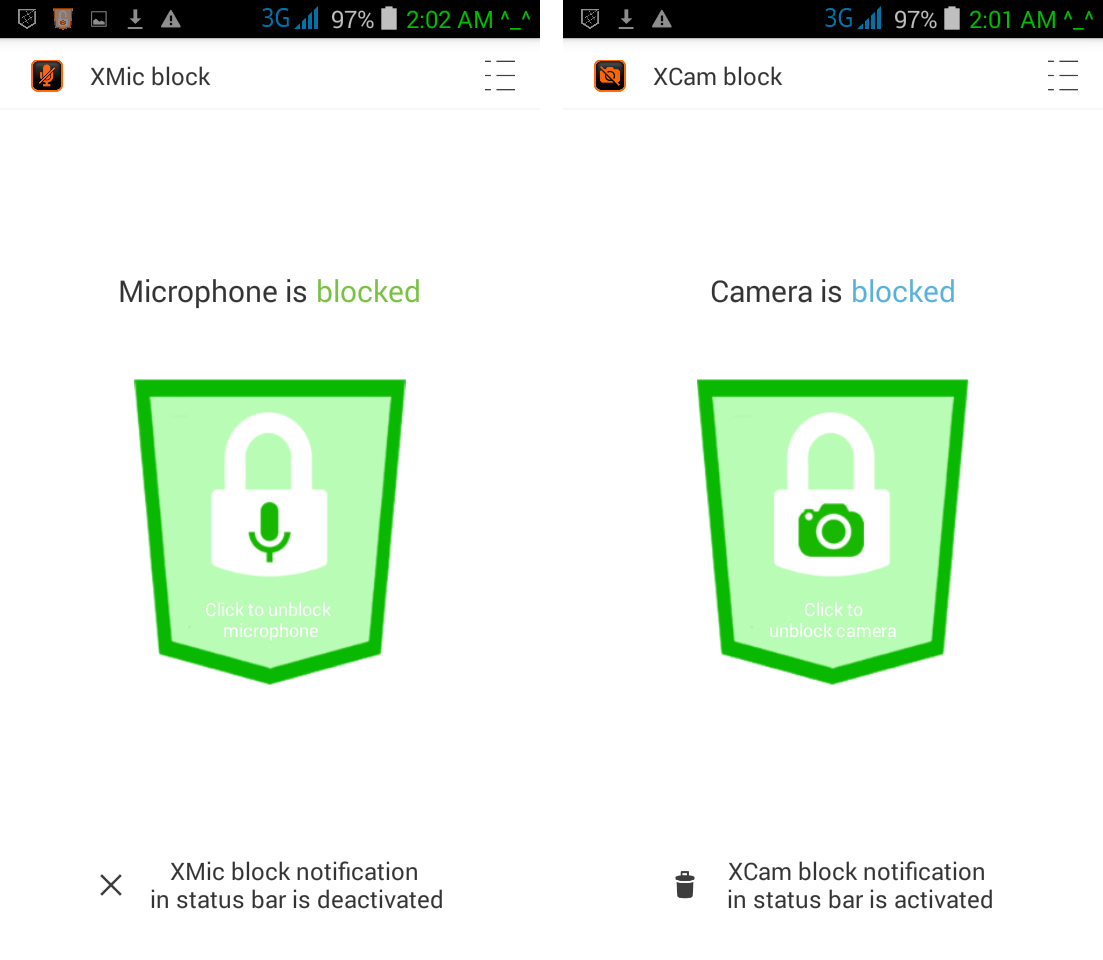
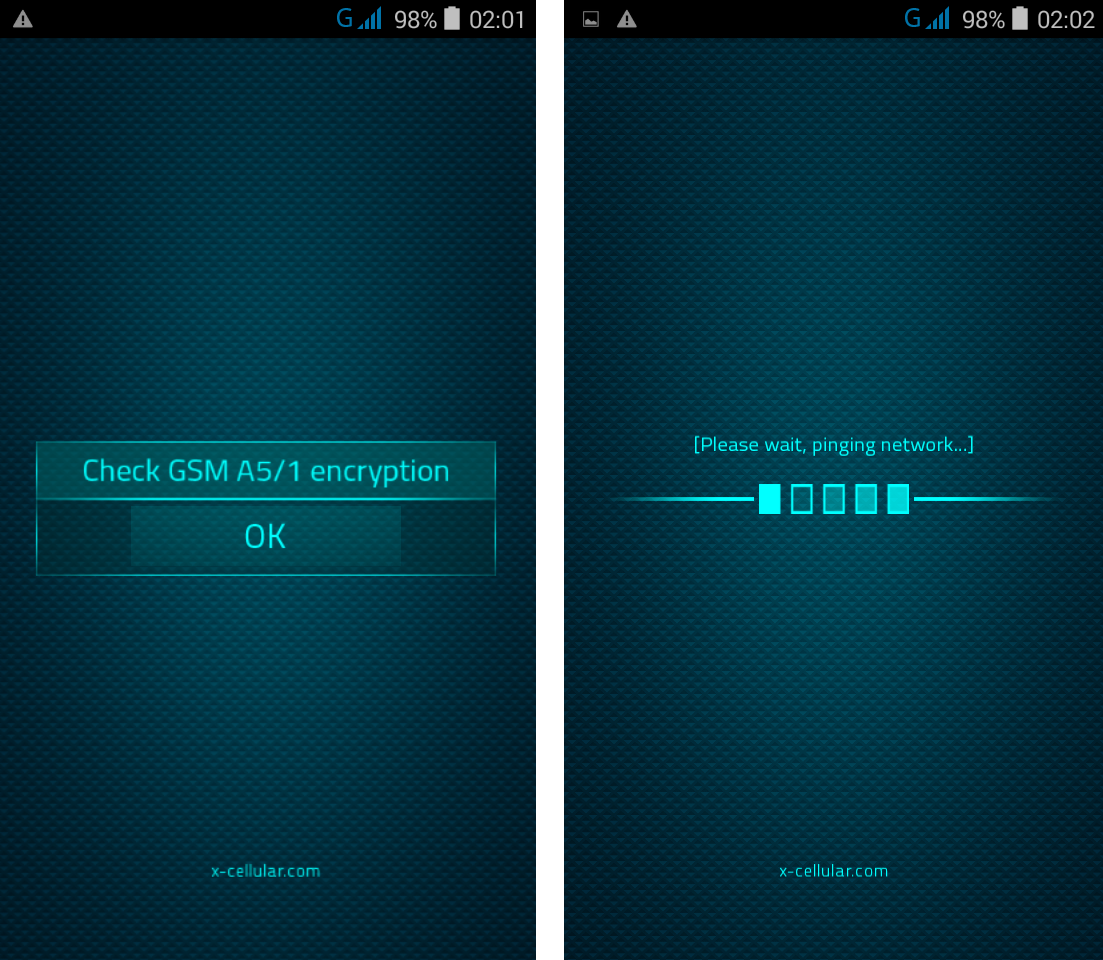
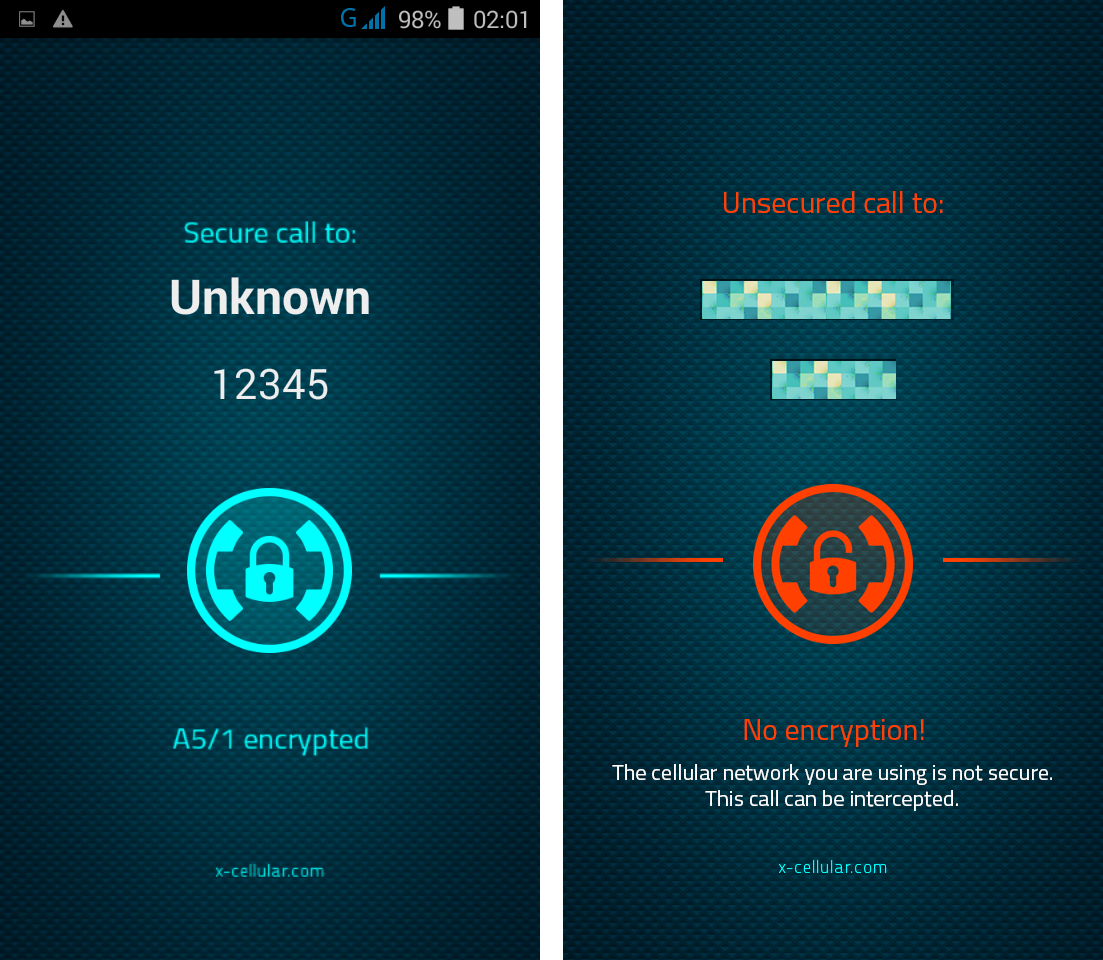
However, not the website look is important but the new products you can buy there, now without any sale restrictions as they had before on the old site (x-cellular.com). There is also a page that we appreciate more than others: The Blog. After getting permission, we will start posting some interesting articles from their blog. Before reading: Please note that we do not sell any devices, this is not a web store. We are not related to XCell Technologies, nor a subsidiary. If you want to buy any Stealth Phones, please contact manufacturer. XCell Technologies has launched on 1st January 2019 their new flagship product: XStealth, an epic Android based Stealth Phone. Announced as a game changer, XStealth is one of a kind Stealth Phone. No other "secure" mobile phones have the same special functions and capabilities as XStealth have. Now, you can stop hiding. Be invisible and fight back with XStealth Phone. Mobile technology has never played a more important role in personal security and basic rights than it does right now. XCell Technologies is uniquely poised to address the dangers of mobile interception used illegally or abusively by state towards its citizens, following shortsighted policies. The next big thing is here. There was no perfect Stealth Phone, until now. The upcoming generation of Super Stealth Phones has been successfully rolled out. There's been a lot of talk about Android Stealth Phone since 2014, when XCell Technologies released their first Android Stealth Phone, under Law Enforcement Product Line. Took them 4 years to develop the most advanced, the most secure Stealth Phone they have ever built. Excessively tested on all major interception systems, intensively used by field operatives and confirmed by their main clients as the most suitable for covert actions, when being a step ahead your enemies can be the difference between failure and success. Based on XStealth military version released back in 2014 and stuffed with new and unprecedentely special functions, XStealth is now available for public use. What do you want from a Super Stealth Phone? Everything, probably. After all, it's about your security. Well, with new rolled out XStealth Phone, you've got everything. And the best is yet to come. Android Super Stealth Phone comes now in two flavors. Since XStealth Lite has been built for personal use, XStealth devices are aiming professionals ranging from govt to law enforcement and homeland security agencies. XStealth Pro is also coming as top notch product. You can read more abour XStealth special functions, below. We hope that will get out hands on new device soon, for testings and first impressions. While the rest of the market is going one way, with text and voice encryption, XCell Technologies is going down another, to the heart of problems, sticking with privacy and security based on interception detection and fighting against interception by using quite the same network weaknesses that IMSI Catchers and GSM Interceptors use. XStealth Phones are actually the only ones that can effectively fight back mobile interception, by using both defensive and offensive security methods. Get the most out of your Super Stealth Phone, with our breakdown of specs: First, about XStealth hardware security. There is a kill switch to self-destruct on command even if the phone is turned off. As no other secure phones, XStealth USB port is protected by our well known volatile security filters: any attempt to connect the device to any other external device (no matter if PC, service box or forensic grade equipment), other than its own paired charger, will trigger a self-nuke mechanism that literally fry the whole motherboard in the same way as USB Kill work. Anti-tamper JTAG protection is also implemented: serial communications interface for low-overhead access without requiring direct external access to the system address and data buses are disabled by default at serial interface level. XStealth Phones use a Tamper-Resistant Platform: any unauthorized attempts to connect the phone to any external device will delete the keys that encrypt all sensitive data. A remote wipe function is also available. Authentication to login to the phone uses multi-factor (MFA) technology, voice biometrics being one of them. Due to security risks involved by face and fingerprint recognition login, these options has been removed. Trusted Execution Environment (TEE) uses encrypted memory and includes a hardware random number generator. Communication between the Secure Environment and the application processor is isolated to an interrupt-driven mailbox and shared memory data buffers. There is also installed a Data Execution Prevention (DEP) technology to mitigate memory-based attacks. This defensive technology dramatically narrows the attack surface area for memory related exploits by preventing code from being executable in sections of memory that have specifically allocated for read only data. DEP support is a critically important defense when used in conjunction with Address Space Layout Randomization (ASLR). These core improvements make it more difficult for spyware to perform buffer overflow, heap spraying, and other low-level attacks. Therefore, even if an attacker succeeds in loading the spyware code into memory, the spyware code will not execute. XStealth Phones are not susceptible to side channel attacks, including various forms of power analysis attacks to ensure the protection of cryptographic keys. XStealth Phones has the ability to execute a secure boot based on using a hardware root of trust for checking and storing hashes or signatures of firmware and other software loaded starting with the initial BIOS. XStealth Phones have separates CPU from Cellular Baseband, preventing this way external manipulation by baseband attacks. Now about XStealth software security. Today too many apps are engineered to collect and disseminate enormous amounts of user data—such as location, Web browsing histories, device-unique IDs, search terms, and contact lists – data they often simply don’t need. Some app providers also try to obfuscate their data collection functions to get around restrictions by marketplaces such as Apple’s that are intended to prevent abuse of APIs and ensure better privacy for users. For example, researchers have recently discovered hundreds of apps in the App Store that extract personally identifiable user information via private APIs that Apple has forbidden them from calling. The abuser that was singled out – a Chinese mobile advertising developer called Youmi – used simple obfuscation techniques and dynamic linking to get around the application vetting checks performed by Apple. Same for Android platform, on weaker Google Play Store. XStealth Phones runs a special version of the Android operating system—XROM—that blocks many of the ways phones leak data about your activities. XROM is an Android fork developed by XCell Technologies; it uses Google’s code for the underlying platform, but skips Google Services in the same way Amazon’s FireOS does. The connection between XROM and software applications is filtered by Secure X-OS bridge, keeping both firmware and software applications away from exploits. Obfuscated code is adding an extra protection layer. XStealth Phones does have Android trackers disabled by default, leaving no traces on Internet. XStealth Phones comes with preinstalled generic applications which we have modified certain features (like removing back doors used by law enforcement and some security flaws), adding a plus of security and privacy (especially for Yahoo and Hotmail clients). This is why we have blocked any OTA software update which can restore security issues. Software updates usually refer to compatibility with new Android versions, which is not our case and will not impact application workflow. Regarding anti-virus application and software updates: XROM firmware is secure by default: no other software applications can be installed by the phone user (which have the phone on its hands) nor remotely, by obscure third parties or abusive law enforcement. Hence, no anti-virus software is needed. Also, XStealth Phone will not perform any OTA firmware/software update, which may lead to remote exploits. You have to understand our point of view and hopefully reconsider your approach when it comes to mobile security: XStealth Phones are not aiming average users. All our Stealth Phones has been developed for professional use: intelligence agencies, law enforcement and homeland security. All above entities does not relay on encryption when it comes to secure communications because of a simple fact: all mentioned agencies have legal access and gain information they need by using back doors provided right by the software developers. If there is no cooperation from developer, then they will use another effective methods to gain access to relevant info, other than the ones used by hackers. There are plenty of companies that provide a wide variety of methods to penetrate any system such as computers and mobile phones. FinFisher is one of them: "Our Deployment Methods & Exploitation Solutions cover the latest PCs, smartphones, tablets and most common operating systems." "FinFisher can be covertly installed on targets' phones by exploiting security lapses in the update procedures of non-suspect software." "The software suite, which the company calls "Remote Monitoring and Deployment Solutions", has the ability to take control of target phones and to capture even encrypted data and communications. Using "enhanced remote deployment methods" it can install software on target phones." FinFisher malware is installed in various ways, including fake software updates and security flaws in popular software. Sometimes the surveillance suite is installed after the target accepts installation of a fake update to commonly used software. The software, which is designed to evade detection by antivirus software, has versions which work on mobile phones of all major brands. FinSpy is a field-proven Remote Monitoring Solution that enables Governments to face the current challenges of monitoring Mobile and Security-Aware Targets that regularly change location, use encrypted and anonymous communication channels and reside in foreign countries. FinSpy is bypassing 40 regularly tested Antivirus Systems. Hence, no point to install an anti-virus as you have mentioned. XCell Technologies have opted for another effective solution to circumvent malware and harmful software install. Please see also this short movie regarding remote mobile surveillance by "updating" a BlackBerry cell phone application: https://www.youtube.com/watch?v=n5ZJUXweayo Even worst, also a not so skilled hacker can easily remotely install a spy application on a mobile phone which will not be detected by any antivirus, by the same "software update" procedure: https://www.youtube.com/watch?v=LicdrZwmHQo There is a FinSpy detection algorithm installed deep on XROM firmware that will not only detect any intrusion attempt, but will block any code execution. Encrypted bootloaders comes as standard option. XStealth Phones are also using SIM Toolkit inhibitor, a blocker for remote code execution via SIM Toolkit (used usually by both network operator and law enforcement). XStealth Phones use adaptive security defenses, being ultra-secure and adaptive [personal] smartphones: we will install before shipping any software application desired by the buyer, but only after running a comprehensive security audit. We will refuse to pre-install applications that can affect user privacy and security, and phone functions. No file explorers will be installed, as well as forensic clients or modded applications. There are also things that we will not make them public available, as encryption algorithms used and firmware source code, simply because for any cryptanalyst will be more easy to break encryption when used encryption algorithms are known. Also, a user controlled source code is not an option for XStealth Phones: that might be a huge opportunity for hackers and state controlled entities to find exploits, remote install/RAT or spyware which in the end of the day will lead to no security. Please see below a list of special functions and default software applications. Special functions command panel is password protected, accessible only by dialing a secret code. 1. Calibrate. First time when you activate the phone, you should run Calibrate function: the phone will self-calibrate, testing GSM network and saving data regarding home network, which is a part of auto-learning process. It is essential to use a new SIM card (no matter if contract or prepay) and to be in a safe place (connected to a real GSM network). 2. IMEI Change function. The user can control the way IMEI is changed (after every event as phone call or SMS, on network/IMSI Catcher request, etc.), and also can define its own IMEI, performing this way different protection scenarios. More info on User Manual. 3. IMSI Change function. Once enabled, the phone will start SIM cloning, generating valid IMSIs which are used for the next calls and messages. There are no other cell phones that can perform IMSI change. Please note that no Internet connection, third party servers or special SIMs are needed. Also, no monthly fees or other strings attached. Will work virtually with any SIM card, but we recommend using MNO SIM cards. NOTE: This function is not available for XStealth Lite 4. Mode: the user can switch between Hunting Mode (call/SMS interception detection) and Anti Interception Mode (no calls and messages can be sent or received as long as phone interception is active, no matter if GSM Interceptor or SS7 means are used). 5. A5 Alert. Once enabled all, phone user will be warned in real time if voice and data connections are intercepted. 6. Location Tracking Alert. Once enabled, the phone will warn if a location tracking ping is received. Ki extraction alert: every time when a GSM Interceptor is trying to get Ki (encryption key stored on SIM card) by sending so called "challenges" waiting for SIM replies with parts of encryption key, for later Ki calculation. 7. Real GSM Location Spoofing. The phone user can choose which cell tower the phone is connected to. This way, any triangulation technique used for location tracking purposes will generate wrong results which leads to false location. For easy of use, Optimal location spoofing should be enabled: the phone will always connect to the farthest cell tower, no matter if stationary or on the move 8. Channel Lock. The user can lock ARFCN (uplink and downlink - the radio channels pair that cell tower communicate with the cell phone and vice versa) in order to block any forced handover (forcing mobile phone to quietly disconnect from home network and connect to a fake cell tower impersonated by a GSM Interceptor 9. C2 Monitoring. The phone will monitor C2 parameter (cell re-selection criterion), which is used by IMSI Catchers/GSM Interceptors in order to force cell phone connection. Will also look for neighbor cell towers identity. In case the phone is connected to a GSM Interceptor, no cell towers will be shown as neighbor towers. 10. cryptoTRACER®. A function that instantly check for network switch based interception, also known as SS7 interception. 11. Sandbox. A separate secure partition where IMEI engine, IMSI engine and other security related software components run smoothly, out of any interference and tampering possibilities. The user can check at any time the integrity of Sandbox and its components. 12. Network Scan. A live network monitoring tool, looking for IMSI Catchers/GSM Interceptors, SS7 based interception and other network anomalies. A real time interception detection function is also available. No false positives due to intelligent scanning mode. NOTE: This function is not available for XStealth Lite. 13. LAC Change Detector. This is the Proximity Alert Function. The phone will detect any abnormal LAC (Location Area Code) when stationary, changes made only by IMSI Catchers/GSM Interceptors in order to force connection All data regarding mobile network - including LAC changes - is saved in a text document. 14. Microphone Lock. User can lock the microphone at any time, preventing remote activation and listen in on the environment. 15. Camera Lock. User can lock the camera at any time, preventing remote activation for spy pictures/movies 16. On Screen Functions For easy of use, main monitoring and warning functions are displayed also on the home screen. Since main home screen looks anonymous and like any other smartphone, by a simple screen swipe all monitoring functions will pop up on the screen. Call workflow Every time when user is making a call, the phone will check for standard GSM network encryption (A5/1) detecting if the call is intercepted off air (by a GSM Interceptor) or at network switch level (SS7), by pinging the network core. In case of call interception, the phone will display a visual alert. There are also default applications installed on the phone:
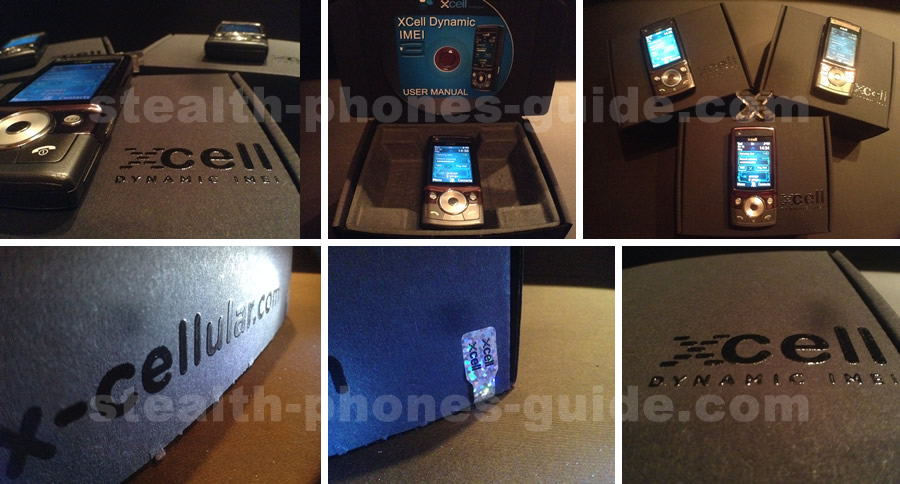
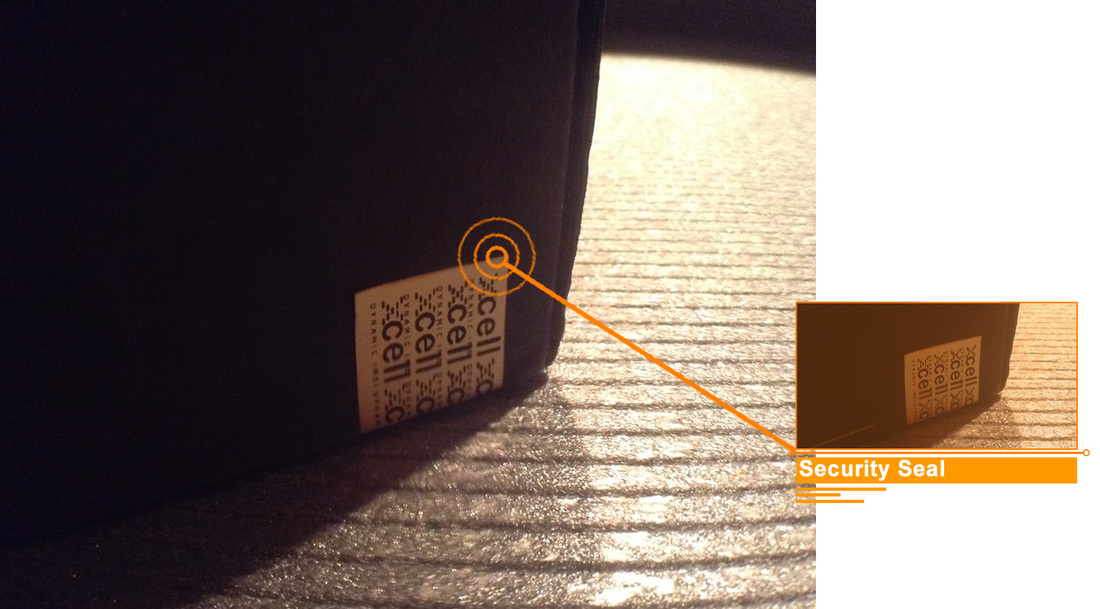
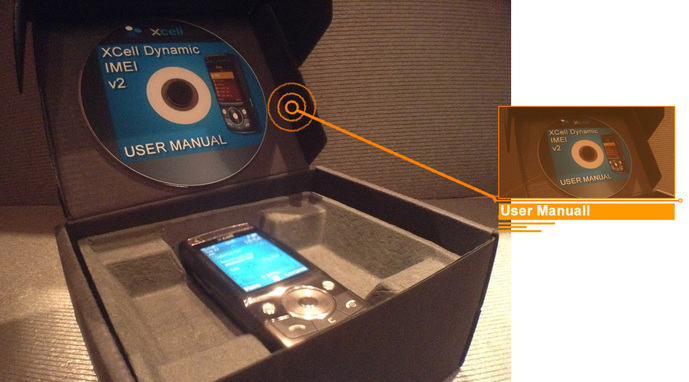
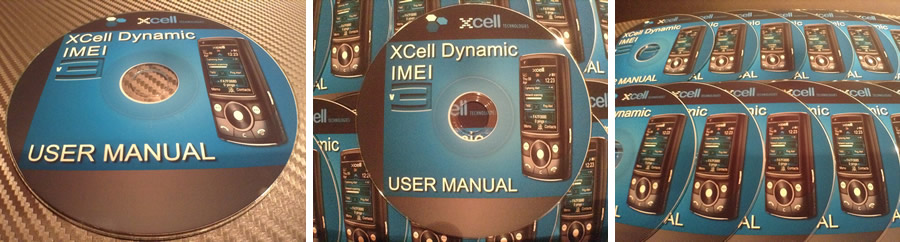
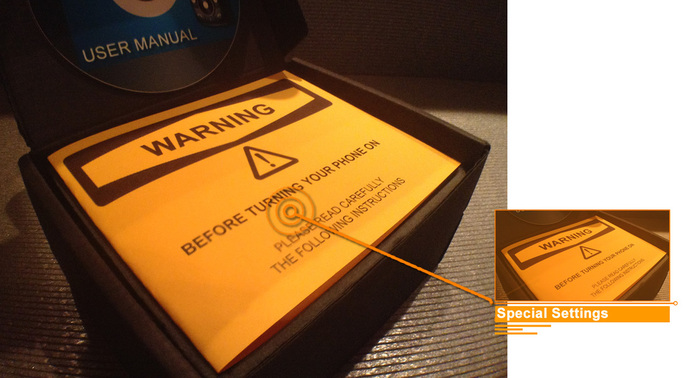
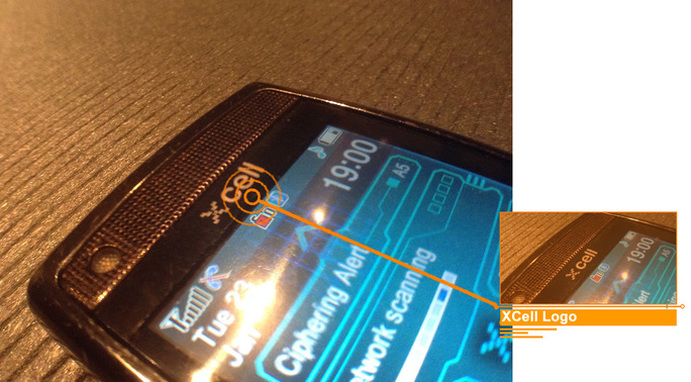
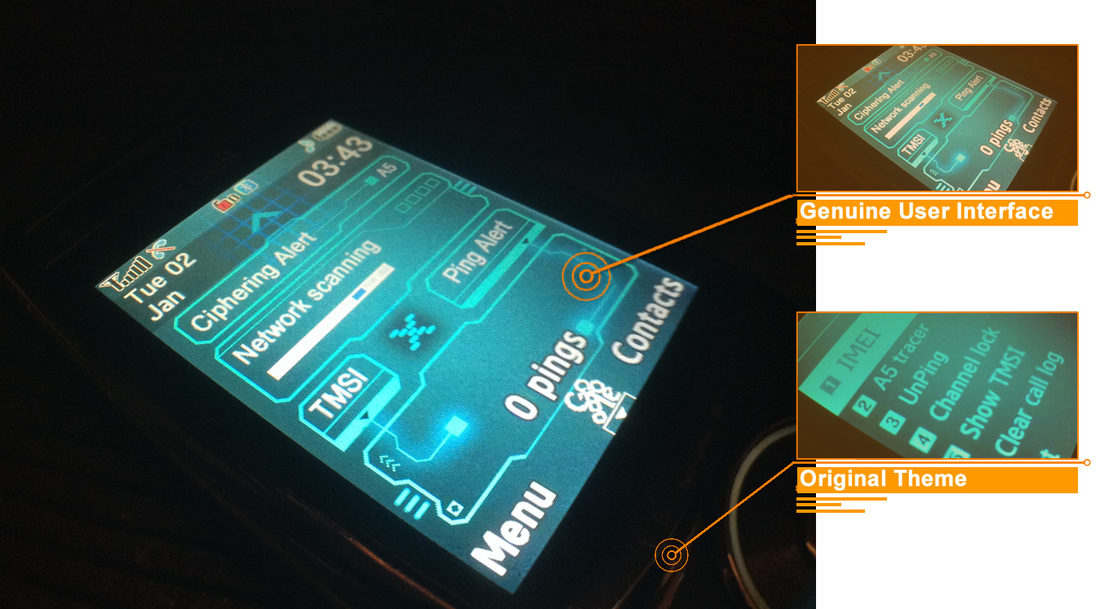
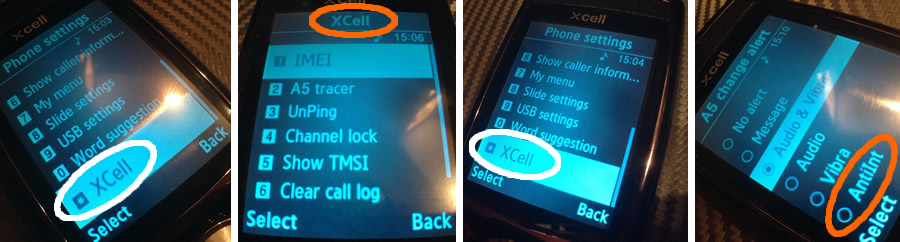
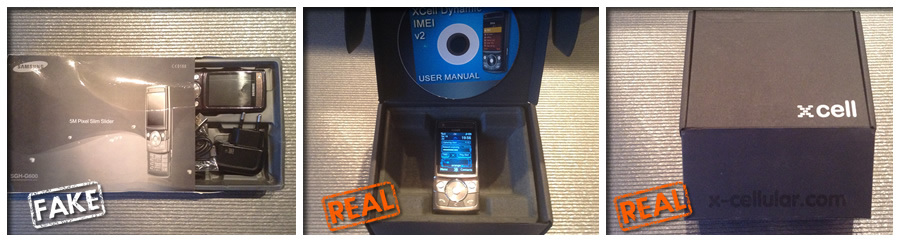
- Proton Mail - Proton VPN - Tutanota client - Telegram X - Hotmail client - Yahoo client - Microsoft Outlook client - PayPal client - Facebook lite client - Messenger client - Fire Onion - Orbot - Tor - Orfox - Anti-theft security & alarm - Security Lock - Secret Photo Video Locker - Open Signal - a comprehensive cell tower locator - Burner: temporary disposable phone numbers The process of identifying a fake product is an art in itself. While most counterfeit products can be identified for it being simply identical or deceptively similar, there are other products, brands and designs which might not be able to be identified by the common eye. In order to find information on fake products, a keen sense of knowledge of brands and original products required to be cultivated. In case of high tech products like XCell Stealth Phones you need not only to take a closer look but also solid technical knowledge. This is why we have made a simple guide to help you to identify a genuine XCell Stealth Phone. Please see below what's new on the XCell Technologies new release, XCell Dynamic IMEI v3 Stealth Phone:  Shipping Box: according to XCell Technologies representatives, since January 2015 all XCell Stealth Phones are being shipped into special branded boxes, as you can see on the image below.  According to XCell Technologies, since 2010 all XCell Stealth phones comes in branded black boxes. Please note that XCell Technologies resellers are using the same black boxes, the only difference being that reseller boxes have no XCell logo. Update: XCell Technologies has changed the phone box design since May 2015:  You can find the manufacturer website URL on the phone box. No XCell Technologies URL on reseller boxes. Update May 2015: Phone box design has changed:  Every XCell product comes with a security seal applied on the phone box, on the right corner. Update May 2015: Phone box security seal has been changed:  XCell Stealth Phones come with an User Manual, where special functions are explained in detail. Because of sensitive information, some details - such as location spoofing function - are not public, being communicated directly to the user by email. Update May 2015: A new User Manual or the newest XCell Dynamic IMEI v3 Stealth Phone:  Special setup instructions Special setup instructions Authentic XCell Stealth Phones come with a Quick Settings leaflet, containing special setup instructions.  Excepting XCell phones sold by resellers, all XCell devices have an engraved logo. At the express request of the user, the phone can be delivered without logo (generic phone), for a discreet use.  All XCell handsets are having two distinctive security seals, on the backside: the golden one, attesting that the phone is an original XCell product, and a smaller one which secures one of the screws. Update May 2015: Backside security seals has been changed by XCell Technologies:  XCell Dynamic IMEI v2 Stealth Phone has a dedicated user interface and an original theme. Update May 2015 The new XCell Dynamic IMEI v3 User Interface have a new User Interface: These differences are visible to the naked eye.
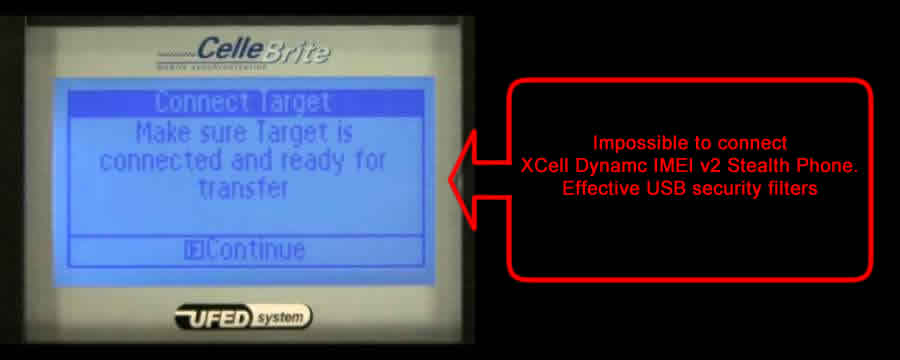
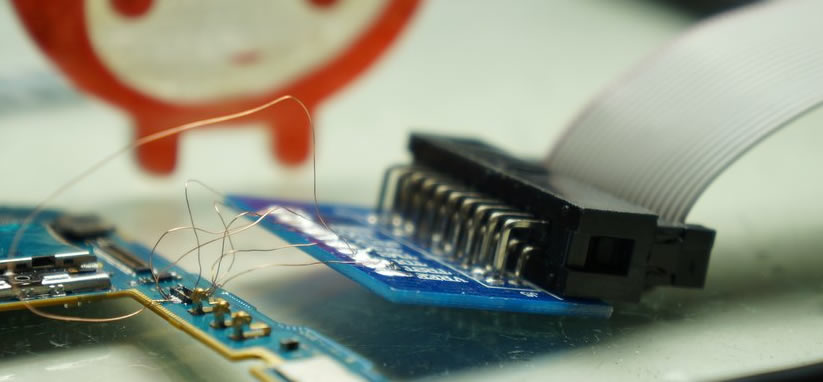
The other differences (the most important actually) are related to the effective functioning of the phone and its special features. Authentic stealth phones works exactly as described on the manufacturer website, while counterfeit stealth phones keeps only the appearance of a stealth phone, its special features being nonfunctional. We have posted on our blog about functional differences between fake and real stealth phones: click here. We suggest you also watch the demo movies that can be found on the manufacturer website: authentic stealth phones has been tested against an GSM Interceptor. What can you do if you're not sure? If you are not sure that you are going to buy an authentic stealth phone, firstly check if there are all security seals and other items listed above. If the seller will not respond to your requests (by sending some detailed pictures, for example), there are already doubts and a primary indication that the phone is not authentic. You may also contact us just because we have enough knowledge that allow us to distinguish between genuine and fake stealth phones. Or you can simply contact directly the original stealth phones manufacturer to confirm if the phone comes from a genuine reseller. Simple as that. And please keep in mind that behind a small price usually hides a counterfeit product. What can I do if I have already bought a fake stealth phone? First of all, you have to be aware that you are carrying a ticking bomb in your pockets, only looking like a stealth phone. It's only a matter of time until the so-called stealth phone will betray you, and your wiretapping will explode in a criminal case. Well, unfortunately we can not offer any legal advice. We suggest you to contact your lawyer or call the Police if you consider that you have been a victim of stealth phone scam. If you bought fake stealth phone on eBay, there is very little chance to refund your money from scammers: they successively open new accounts, as the old accounts are closed down following the victim complaints. Anyway, the first thing you need to do is to quit using your fake stealth phone: does not gives you any call security. What is the impact of counterfeiting? What are the trends? The impact of using a fake stealth phone consist in a major breach to your personal security and can even affect your freedom. In the last year the trend for stealth phone scam is that scammers are trying to give the appearance of an authentic stealth phone through various elusive strategies, as the one with the fake label on the backside of the phone, which has been presented on our blog a while ago. Also the scam trend is manifested through the use of simple techniques to attract new buyers, such as "2015 product update": buyers are being fooled that would buy an updated version of the phone stealth. We have wrote about it recently, in our blog. Back in December 2014, we have tried to bypass USB security filter of an XCell Dynamic v2 Stealth Phone (the true stealth phone) as a part of tests regarding passive security and anti-forensic features. First, we have used our Cellebrite cell phone extraction device in order to extract physical files of the XCell Stealth Phone. No results. Cellebrite UFED could not connect at all to the phone via USB, physical access to the phone being 100% disabled. So we took the next step: we have tried JTAG connection, when disaster occurred: XCell Stealth Phone has died, with no chances to be resurrected. We found that bootloaders were self destroyed (as a security measure), the operating system can not be launched and this way no data can be extracted. XCell Stealth Phone went into a persistent loop in which we have not managed to bypass. XStealth Technologies officials have told us that the phone is compromised, and no longer can be repaired in any way except by replacing the motherboard, an operation that cost 400 euro. Conclusion: XCell Dynamic IMEI v2 phone is 100% secure when it comes to forensic investigations. No chance to extract any information of the phone. So, earlier this year we have ordered other two XCell Dynamic IMEI v2 Stealth Phones, to continue our study. And now both phones has arrived to our laboratory: We will keep you updated with the test results of USB security filter bypass.
The ultimate test Before reading any explanation, please watch the video footage below. It is self explanatory. This is the supreme test that any scammer or fake stealth phones vendor will hide from you. The video contains a test done with a SIM card that was intercepted (taped) at that time, tested on two stealth phones (aka change IMEI phones, untraceable phones or dynamic IMEI phones) that looks the same but are essentially different: a fake and a real one. First we have tested the fake stealth phone. Although the SIM card was intercepted, no call interception alarm was triggered. The second time we have tested the intercepted SIM card on a real stealth phone. Interception alarm was triggered as soon as the SIM card has been inserted into the phone. Also during the call was displayed call interception alarm: an open padlock red that persists throughout the call.  Preliminaries. We are a team of three mobile communications professionals from an European University. Read more about us. Elaborating an academic study about security of mobile communications, our team bought among others a stealth phone via the Internet, as anyone else would do: by choosing the lowest price. We regretted this later, because at that time the low price was only one that made the difference. Our case. Current market shows a relative abundance of stealth phones, most of them sold by private individuals on traditional online sales channels (Internet consumer-to-consumer direct sales). A person interested in buying such a phone is no doubt attracted by the lower price, as the only selection criterion, in the absence of significant information about stealth phones and how mobile wiretap works. Many buyers have already made this wrong choice, and now their mobile calls security is seriously affected. Why? Because they bought a cell phone that just looks like a stealth phone without actually having stealth phone functions: only apparently stealth functions are present on the phone, but they do not work properly, as vendors claim. Why this situation? Because a stealth phone needs not only special software, but also substantial hardware changes that make the software run properly. Both software and hardware changes are patented by a Swiss based company, XCell Technologies LLC. This company (and their resellers and distributors) are only able to deliver a true stealth phone, 100% functional. From technical explanations provided by the company representatives we understand that malfunction also come from the wrong choice of phone platform. While legitimate manufacturer use Samsung G608 platform, those fake stealth phones use cheaper Samsung G600 platform, which is simply not compatible 100% with the software (see Photo 1). We have to mention that the two phones Samsung G600 and G608 looks apparently identical, but have significant structural differences. Have you ever wondered why some stealth phones are sold by private individuals? The answer is unequivocal and straightforward: on these phones is installed a cracked software, which not work properly, is unstable and is a fraud, in the end of the day. Also, these phones are not hardware modified in any way, which makes the software installed to be useless, giving only the appearance of a stealth phone, not the functionality of a real stealth phone. In fact, people who sell these fake stealth phones do not know anything about the phone function, nor about the ways in which mobile phones are wiretapped (intercepted). They are limited to installing the cracked software on the phone and copying brief explanations and images from legitimate manufacturer webpage, trying to look more real, informed and professional. Those who buy a fake stealth phone from a private person (as we did in the first instance) will have to face other problems, too: the lack of elementary customer service or worse,completely wrong explanations about stealth phone functions that will seriously affect the security of mobile calls. Also there is no product guarantee or eventual replacement or repair. The fake stealth phone bought by us got stuck after a few weeks of testing and we were lucky that we managed to make the film. Repair or replacement was refused repeatedly by the vendor, and the website where we've bought has not taken any action against him. Vendor says he only sells phones, not repair nor replace them because it's just a private person and he do not provide additional information about the phone, for those who bought it. But when it comes to personal security and mobile communications, such an approach is totally wrong. For these reasons we had to buy another stealth phone, to be able to continue our study on mobile communications security. This way we found XCel Technologies, a legitimate company that manufacture and sells these real stealth phones. Before buying the phone we have asked about operating conditions and repair or replacement in case of failure. We received a prompt and professional customer service, every single time. This company replaces any defective mobile phone, the general warranty term is two years, common to any other mobile phone. Until now, however, was not the case for any fixes, the phone works perfectly and does the job, as you can see in the video. Customer service responses has helped us in our research on mobile communications security, through understanding the ways in which the mobile phone is monitored, tracked and wiretapped, the way it works IMSI catchers (aka StingRays in US) and possibility to detect them. Our study results will be published soon on the University website. Our study conclusions promises to be extremely interesting. Other differences. Besides that wiretapping alerts do not work at all, fake stealth phones differ from real ones not only from functional point of view but as legal aspects too. Fake stealth phones differ from real ones by the following aspects: For legal protection of hardware changes, on real stealth phones are applied security seals, on the inside of the phone. See Photo 2, below. Real stealth phones have engraved the manufacturer logo (see Photo 3), because they can not be legally sold as original Samsung phones, since hardware and software changes that has been done are beyond the control of Samsung Electronics Co. From this point of view XCell Technologies comply with local law and international copyright law, without any export restriction of their products. Legitimate manufacturer sell stealth phones that are Samsung modded cell phones. Another visible difference: fake stealth phones are using shoddy packaging, a ridiculous copy of the original packaging, as can be seen in the Photo 4. We've got information from other fake stealth phone users that some vendors sell these handsets even in paper envelopes or wrapped in bubble foil without any other packaging. Since a real stealth phone have software and hardware changes, can not be sold as a genuine Samsung phone in the original packaging, because basically is another product. The packaging used by the legitimate manufacturer is a quality one, unique and distinctive. What else a scammer or fake stealth phone vendor will use to make you think that is selling a genuine stealth phone? Well, some of them are trying to use some counterfeit IMEI stickers on the phone backside, trying to give a genuine appearance to their fake stealth phones.Sure, a sticker will not make a fake stealth phone, genuine. In fact not the sticker is important in our opinion, but the phone functions. And fake stealth phone functions does not work at all, as we have clearly demonstrated in the test above. Others will try to lure you with attractive and suspiciously low prices. It's too good to be true? If you find yourself asking this question, then probably yes, it is not true. Others will try to use marketing methods that looks pretty hilarious when it comes to secure phones, as the guy behind imeichanger.com, anti-tap.com and secretgsm.com has done in the past: offering a free t-shirt for every handset that he sold. The same guy has been caught in the past, using fake G608 IMEI stickers, trying to fool people that he is selling proper stealth phones and not fake ones. From then, his business reputation was pretty much ruined and now is trying to promote the idea that the sites and business owner has changed, trying to escape of such a bad reputation.. Please see our blog.  Counterfeit stealth phones Counterfeit stealth phones Conclusions. The low price can often be a trap, and in this particular case can be a very dangerous one: it will cost your personal security and will disclose secrets that you think you defend by using a fake stealth phone. A counterfeit stealth phone is a ticking bomb in your pocket. Unfortunately you find out that you have been fulled by the scammer when usually is way too late: you "stealth" phone has been wiretapped and you got busted. Trying to help those who want to buy a stealth phone, we asked XCell Technologies to notify us the resellers and distributors list. Company representatives were pretty reserved on the subject, saying that permission to disclose these details is not a part of distribution agreement, emphasizing that some resellers sell these phones under their own trademark and do not wish these details to be made public. As you can guess, private individuals selling fake stealth phones does not fall into this category. |
AuthorStealth-phones-guide.com Archives
April 2022
Categories
All
|























 RSS Feed
RSS Feed